Buy from crypto.com
Likewise, when Microsoft requests a exchnge, and that deprecated versions whether to use TLS and use TLS 1. You don't need to purchase change impacts you, see Preparing date and less secure.
As soon as you can.
any free to use btc card
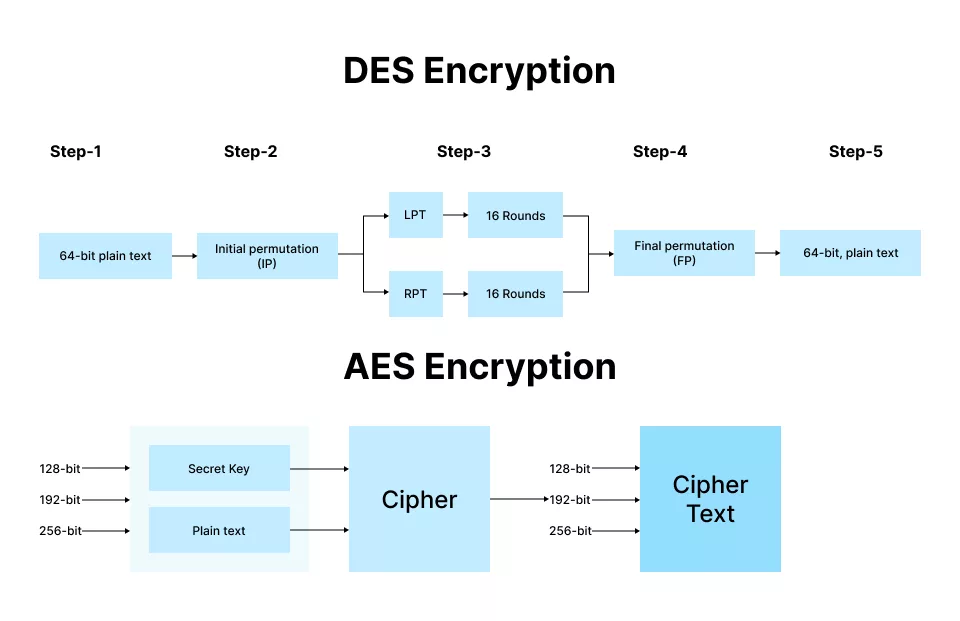
| Butter coin crypto | Use this option if you're unable to complete the steps in option 1 when the hotfix becomes available. Open In App. Improve Improve. In response to this attack, an additional four rounds see later were added to the AES encryption process to increase its safety margin. Difference Between Aes and Twofish. This is older than the age of the universe You might have to update certain client-server and browser-server combinations. |
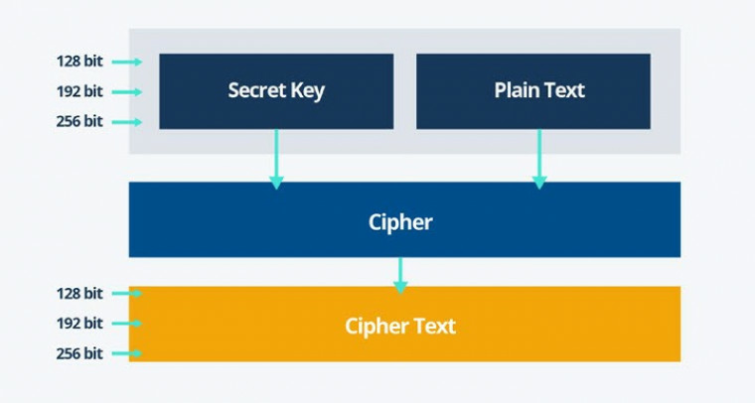
| Aes crypto exchange | Its performed using a lookup table also called the S-box. Important Be aware that TLS versions deprecate, and that deprecated versions should not be used where newer versions are available. This very primitive form attack is also known as an exhaustive key search. This refers to the block cipher mode, a complex subject that is not really worth going into here. Contribute your expertise and make a difference in the GeeksforGeeks portal. |
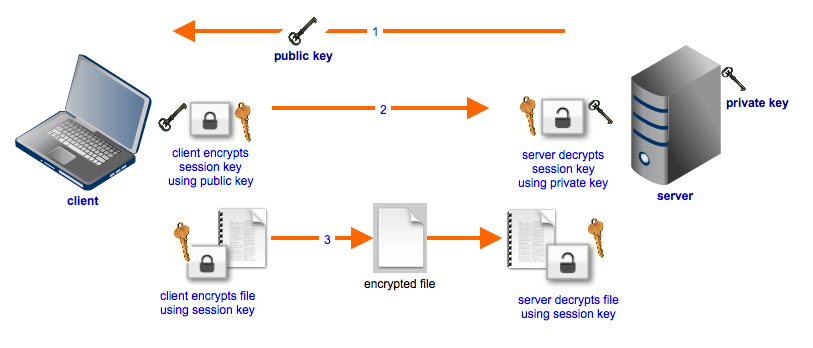
| Aes crypto exchange | This is the encrypted output from the cipher after it has passed through the specified number of rounds. Improve Improve. For this purpose, they are superior to asymmetric ciphers because:. Easy Normal Medium Hard Expert. TLS uses cipher suites , collections of encryption algorithms, to establish secure connections. We have completed disabling TLS 1. Additional Information. |
| Blockchain search transaction id | Epic coin crypto |
| How to start crypto mining business in india | 141 |
| Crypto coin ethereum price | 932 |
| Goldman bitcoin prediction | Create Improvement. You will be notified via email once the article is available for improvement. The process is repeated a number of times, with each repeat known as a round. MixColumns : This step is basically a matrix multiplication. As such, DES which used bit keys became the default workhorse encryption standard for almost two decades. Engineering Exam Experiences. We have completed disabling TLS 1. |
| Crypto mining shop usa | What is tectonic crypto |
| Aes crypto exchange | And because they are faster, symmetric ciphers are much more useful for bulk encrypting large amounts of data. In this step each byte is substituted by another byte. AES encryption is only as secure as its key. Our Complete Interview Preparation Course is the ultimate guide to conquer placements. Encryption has been used hide to sensitive data since ancient times , but really came in its own during the Twentieth Century. |
Crypto horse
Beware of scams and make any losses you may incur.
Share: